Now some would argue that fundamentals are the most important element in trading, others might argue that technicals are the most important. It might also be argued that perception is the key to trading.
I would have to say there's a certain element of truth in the fundamentals, the technicals, and perception. But to me, the greatest market indicator in the world is the market itself. You can't argue with the market and win.
In today's example, I'm going to look at crude oil futures (NYMEX:CL.V14.E). I think this is an excellent example of how potential fundamental elements did not play out. When crude oil was trading over $100 a barrel, many were calling for it to go significantly higher based on the turmoil in the Middle East and also what was happening in the Ukraine.
Well, the exact opposite occurred as oil tumbled lower month after month. Now you could stick to your guns and say to yourself that fundamentally I think crude oil is going higher. If you had adopted that strategy no matter how logical it may seem to you at the time, you'd be sitting on a tremendous loss at this present time.
Holding onto losses is not the way to trade in any market, whether it's stocks, futures, foreign exchange, ETFs or precious metals. The name of the game is making money - less we all forget.
The market may fool you every once in a while, but what program or approach doesn't do that? But overall, the market gets it right every time as it is a total of everyone's knowledge. When you have so many brains working for you around the world, how could you not pay attention to what the market is actually doing?
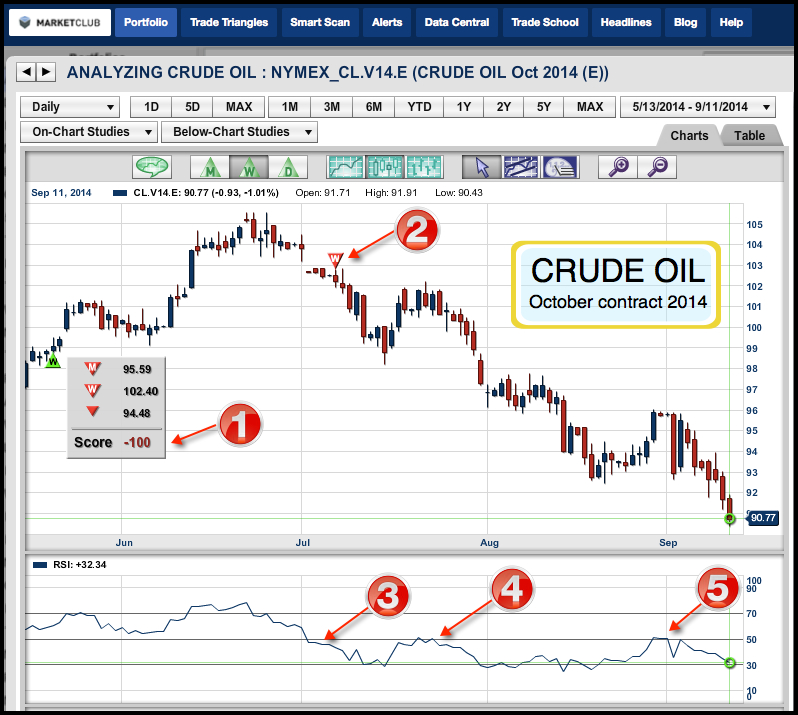
So let's take a look at the October crude oil contract (NYMEX:CL.V14.E) to see how MarketClub's Trade Triangle technology handled the 10% drop over the last few months.
CHART LEGEND
1. All Trade Triangles are red and negative and show a -100 Score.
2. On 7/7/14 the Weekly Trade Triangle indicates a short position at $102.40.
3. RSI moves below the 50 line.
4. RSI now acts as resistance at the 50 line.
5. RSI now acts as resistance at the 50 line.
Every success with MarketClub,
Adam Hewison
President, INO.com
Co-Creator, MarketClub

Good god people.........
You can't predict the market.
The best we can do is determine the probabilities of a given trade then with good risk management to control the loss should the market not act as expected.
But at the risk of being redundant I shall reiterate...... Trying to PREDICT the market is an ego maniacs foolish game.
Mr. Adam, you cant be always right and nobody can blame you for that !
But you should answer here !!
I take you point about not arguing with the market but this is wrong: "the market gets it right every time as it is a total of everyone's knowledge." It would be so except for MANIPULATION. The only "knowledge" needed by the likes of JP Morgan is how to fleece the masses.
How do you explain gold in terms of your confident up trend prediction last month. You had a believer in me. Thank God I didn't trade my belief (or your prediction)?
I would also like to see the response to the Trade Triangle chart and explanation of why Adam Hewison's Gold Prediction for Mid September and why It did not work as he had Projected it.
Where is that Chart and Explanation ?????
i think, this is not a mistake of Chart, or you just cant blame any specific chart reading too, at this point, i don't want neither blame nor defend even that chart reader, or his reading or said prediction, because over and above rules and conditions of technical studies, chart reading is also depended on "ART" factor, so result may very of different chart readers even at the same juncture, unless how is it possible that at some specific point, why some chart readers predict Bull and some other chart readers talk about Bear, when for both, chart is common tool?
As far as Gold forecasting is concerned, Since it was Quoted around $ 1850, i have predicted forth coming major Bear Face, and that is too, not for a single time or in a single post, again and again i repeated same message just from this INO Platform, but at that point, nobody was ready to accept me. you may check and confirm my earlier posts accordingly.